Payment fraud detection is, at its core, your business's digital security guard. It's the system you put in place to analyze every incoming payment, sorting out legitimate customers from fraudsters who are trying to use stolen card details or other sneaky tactics. Without it, you're leaving the door wide open to revenue loss and painful chargebacks.
Understanding Payment Fraud and Its Growing Impact
Think of payment fraud as a silent thief that's constantly trying to skim profits from your online business. What might have once been a minor nuisance has grown into a major operational headache for companies of all sizes. It acts like a hidden tax on your business, siphoning revenue, tying up your team's valuable time, and eroding the trust you've built with your customers.
The scale of this problem is staggering. Global merchants are on track to lose an estimated $66.4 billion to eCommerce payment fraud in 2026 alone. This isn't just a background statistic; it's a critical challenge that demands a real defense, especially as fraud attacks get more sophisticated and coordinated. For those of us selling digital goods, the threat is even more direct, with projected losses hitting $12.4 billion annually.

More Than Just Lost Revenue
The initial dollar amount lost in a fraudulent transaction is just the tip of the iceberg. The real damage from payment fraud creates ripples across your entire operation.
- Chargeback Fees: When a customer disputes a charge, you don't just refund the money. Card networks hit you with extra penalty fees for every chargeback.
- Operational Drain: Your team gets bogged down investigating suspicious orders and drowning in dispute paperwork. That's time they could have spent growing the business.
- Customer Friction: On the flip side, being too aggressive with fraud filters can backfire. Accidentally blocking a good customer, a "false positive", creates a terrible checkout experience and costs you a sale.
To really get a handle on this, it's worth digging into the specific risks of fraud that online businesses, especially high-risk merchants, are up against.
The core challenge for any online business today is to create a seamless, frictionless checkout for good customers while building an iron-clad defense against increasingly sophisticated criminals.
Common Types of Payment Fraud
Before you can fight fraud, you need to know what you're up against. Fraudsters use a variety of methods, each with its own tells and targets.
Here’s a quick rundown of the most common types of payment fraud you're likely to encounter:
Fraud TypeDescriptionPrimary TargetCard-Not-Present (CNP) FraudThe classic. Fraudsters use stolen credit card numbers to make purchases online, over the phone, or by mail.Any eCommerce business, especially those with high-value goods.Account Takeover (ATO)Criminals gain unauthorized access to a legitimate user's account and use saved payment methods to make purchases.Businesses with user accounts, subscriptions, and stored payment info.Friendly FraudA legitimate customer makes a purchase and then initiates a chargeback, claiming the transaction was fraudulent to get a refund.Digital goods, subscriptions, and services where delivery isn't physical.Refund FraudA fraudster uses various tactics, like returning a different item or claiming a purchased item was never delivered, to get a refund while keeping the product.Retailers with generous return policies, especially for physical goods.
Understanding these different attack vectors is the first step in building a detection strategy that can spot them before they cause damage.
The Challenge for Modern Payment Solutions
This entire problem becomes even more critical for companies that use modern payment models. For example, we are the reference for card payments with stablecoin payouts. Our simple API lets any business accept global card payments with payouts settled directly in USDC. Our model is built for speed and worldwide access, but that means our approach to fraud detection has to be just as modern to protect both our merchants and their customers.
When you're building a payment stack, you have to think about security from day one. You can see how this fits into the bigger picture in our guide on choosing a payment gateway.
For businesses selling digital products, subscriptions, or monetizing online communities on platforms like Discord and Telegram, the stakes are even higher. Transactions are instant and irreversible, making them a magnet for fraudsters. We also offer native integrations for these platforms. In this world, a rock-solid fraud detection system isn't just a nice-to-have feature; it's a fundamental requirement for keeping your revenue safe as you scale.
How Fraudsters Use AI to Evade Old Defenses
The days when fraud was just about swiping a stolen credit card number are long gone. We're now in a constant battle where fraudsters are weaponizing artificial intelligence to launch sophisticated attacks that simply walk past outdated security measures. This isn't just about committing fraud faster; it's about making it smarter and far more convincing.
Think of traditional, rule-based fraud systems as a nightclub bouncer with a list of known troublemakers. They're great at stopping people they've seen before. But modern fraudsters aren't on that list, they use AI to create brand-new identities or disguise their attacks in ways the bouncer has never been trained to look for.
The Rise of Synthetic Identity Fraud
One of the most insidious new threats is synthetic identity fraud. Instead of stealing one person's complete identity, criminals use AI to stitch together bits and pieces of real and fake information. They might combine a real, leaked social security number with a completely made-up name, address, and date of birth.
The result is a "synthetic" person who looks completely legitimate to a background check or an account opening process. These AI-generated profiles can open bank accounts, build a credit history over months, and then "bust out" by maxing out credit lines or making huge fraudulent purchases before vanishing. For a fraud detection system, they're ghosts in the machine, impossible to flag because they don't match any single stolen identity.
AI as a Force Multiplier for Criminals
Beyond creating entirely new fraud methods, AI makes old-school tactics exponentially more powerful. The emergence of new technologies like AI agent crypto payments also shows how automation is reshaping the payment world for everyone, including those with malicious intent.
Here’s how fraudsters are using AI to scale their operations:
- Attack Automation: AI bots can run thousands of fraudulent transactions per minute across hundreds of websites. They can test massive lists of stolen credentials or probe for system vulnerabilities at a speed no human team could ever match.
- Intelligent Evasion: These AI models learn what triggers your defenses. If a system starts blocking small purchases from a certain country, the AI can instantly pivot its strategy, for example, by changing IP addresses, transaction amounts, or user agent strings to fly under the radar.
- Enhanced Social Engineering: Generative AI allows criminals to craft incredibly convincing phishing emails and scam texts at scale. These messages are personalized and free of the usual grammatical errors, making them far more likely to trick even cautious users into handing over their passwords or financial details.
The numbers don't lie. A staggering 71% of U.S. companies reported a spike in AI-driven fraud attacks in 2025. This isn't a fluke; it’s a direct result of criminals gaining access to sophisticated tools. Deepfakes now make up 40% of biometric fraud attempts, turning what was once a secure verification method into a new battleground. You can get a deeper look at what’s coming by reading expert takes on future fraud trends.
The nature of the threat has fundamentally changed. Criminals are no longer just breaking down the door; they're using AI to build their own keys, making modern payment fraud detection an absolute necessity for survival.
It’s clear that trying to fight today's AI-powered fraud with yesterday's static rulebooks is a losing proposition. To stay protected, businesses need a new generation of defenses that can adapt, learn, and react in real time.
The Essential Signals for Accurate Fraud Detection
To really get a handle on payment fraud, you have to know what to look for. Think about it this way: every single transaction tells a story, and a good fraud detection system is an expert at reading it. It quickly gathers clues, we call them signals, to figure out if a purchase is legit or not. These are the same signals that let an automated system make a judgment call in a fraction of a second.

These signals fall into four key buckets. Each one gives you a different piece of the puzzle, and when you put them all together, you get a much clearer picture of the risk involved.
Transactional Data: The What and When
The first and most obvious clues come from the transaction itself. This is the basic context of the purchase, and while it might seem simple, these signals are often the very first sign that something is off.
Key transactional signals include:
- Purchase Amount: Is the order value way out of line with what you normally see? A fraudster looking for a quick score might try to max out a stolen card with one big purchase.
- Time of Day: If a customer who usually buys things during their lunch break suddenly makes a purchase at 3 AM, that could mean their account has been compromised.
- Order Velocity: How many times has this person tried to buy something in the last hour? A flurry of attempts is a classic sign of a bot trying to test a list of stolen card numbers.
- Shipping vs. Billing Address: A mismatch here is a well-known red flag. It’s especially suspicious if the shipping address points to a high-risk location or a freight forwarder.
These data points are the absolute bedrock of any fraud analysis.
Behavioral Data: The How
Modern systems go beyond what is being bought and look at how the user is navigating the checkout process. This is where behavioral biometrics shine, giving you a surprisingly deep look into whether the person on the other side of the screen is a real customer or a fraudster's script. These signals are incredibly tough for criminals to mimic.
Behavioral signals work in the background, analyzing things like how fast someone types, the way they move their mouse, or even the pressure they use on a touchscreen. This lets a system confirm a user’s identity without making them jump through any extra hoops.
Think about it: a real customer might wander through a few product pages, copy and paste a discount code, and then pause for a moment before typing in their credit card number. A bot, on the other hand, will often paste all the information into the fields instantly, a dead giveaway that it’s not human. This kind of analysis is fantastic for spotting automation.
Device and Network Data: The Where and With What
Every person who visits your site leaves a digital trail from their specific device and network. This information helps you connect the dots between transactions that might seem unrelated at first, making it easier to spot coordinated attacks.
Important signals in this category are:
- IP Address and Geolocation: Does the user's IP address make sense for their billing country? If someone’s location suddenly jumps from the US to Eastern Europe in a matter of minutes, that’s highly suspicious.
- Device Fingerprinting: This is a neat technique that creates a unique ID for a user's device based on its browser, operating system, and hardware. If you see dozens of "different" customers all coming from a device with the exact same fingerprint, you've likely found one fraudster with many stolen identities.
- Use of Proxies or VPNs: While people use services like VPNs for legitimate privacy reasons, their use can also be a sign that someone is trying to cover their tracks and hide their real location.
By digging into these signals, a system can tell when a fraudster is trying to operate from the shadows.
Historical Data: The Who and How Often
Finally, the system considers a customer’s relationship with your business. A loyal customer with a long history of good orders has a completely different risk profile than someone you’ve never seen before. This historical context is crucial for avoiding false positives, that is, blocking legitimate customers, and giving your best customers the frictionless experience they deserve.
For example, a platform that processes payments, like our API that lets businesses accept cards and get paid in USDC, needs to build a rich historical profile on each user to make smart decisions. The same goes for our native integrations with Discord and Telegram, where a user's subscription history is a key input for assessing risk.
The Core Techniques of Fraud Detection Systems
Once you’ve collected the key signals from a transaction, it’s time to put them to work. The truth is, there's no single silver bullet for stopping fraud. A truly effective defense layers several techniques, blending the raw speed of simple rules with the deep intelligence of machine learning to make smart decisions in the blink of an eye.
Think of it less like a single padlock and more like a layered security system for your business. You have the obvious tripwires on doors and windows (your basic rules), but you also have intelligent cameras that learn what's normal and what's not (your machine learning models). Each piece plays a different role, and together they form a powerful, adaptive barrier.
Rule-Based Systems: The Frontline Defense
Rule-based systems are the bedrock of most fraud detection setups. They're fast, straightforward, and operate on simple "if-then" logic. You define the rules, and the system executes them instantly.
A classic rule might be: "IF a card is from the US, BUT the IP address is from Vietnam, THEN flag for review." These systems are fantastic for catching well-known, obvious fraud patterns. They act as a quick, essential filter. Their main drawback? They're rigid. Fraudsters are creative, and once they figure out your rules, they'll find a way to work around them.
Machine Learning: Finding the Unseen Threats
This is where the inflexibility of rules becomes a problem. Sophisticated fraud doesn't always follow a clear pattern. That's why modern systems lean heavily on machine learning (ML). Instead of being programmed with a static list of rules, ML models are trained on vast oceans of historical transaction data.
By analyzing millions of past payments, both fraudulent and legitimate, these models learn to spot the subtle, almost invisible connections that signal fraud. They see the patterns a human analyst might miss. This means they can adapt as fraudsters change their tactics, without anyone needing to write a new rule.
More importantly, ML understands nuance. It can distinguish between a legitimate customer making a large purchase on vacation and a fraudster using a stolen card from an unusual location. This dramatically cuts down on false positives, those frustrating moments when you block a good customer by mistake. Instead of a simple pass/fail grade, ML provides a dynamic risk score for every transaction, giving you the flexibility to handle borderline cases with more care.
This is exactly how our own API operates when helping businesses accept card payments and settle in USDC. It analyzes dozens of signals in real-time to generate a risk assessment, securing every payment. You can get a much deeper look into how these systems function by reading our complete guide on how payment fraud systems work.
Device Fingerprinting and Behavioral Analysis
Fraud detection isn't just about the payment data anymore. It’s also about who is making the purchase and how they are doing it.
Device fingerprinting is a clever technique that creates a unique ID for a user's phone or computer based on its specific attributes, things like operating system, browser version, screen resolution, and installed fonts. If you suddenly see twenty different orders placed from "different" customers who all share the exact same device fingerprint, you've likely found a fraudster using a stack of stolen cards.
Behavioral analysis takes this a step further by quietly observing how a user interacts with your website or app. It looks at things like typing cadence, mouse movements, or how quickly a user pastes information into a form. A real customer browsing your store behaves very differently from an automated script or a fraudster rushing to use a stolen card before it's cancelled. These systems spot that difference instantly.
One of the fastest-growing headaches for merchants isn't stolen cards, but fraud committed by legitimate customers. So-called "friendly fraud" and first-party misuse are on the rise, with a recent report finding that between 62% and 64% of merchants have seen an increase. This is where a customer makes a legitimate purchase and then disputes the charge with their bank. It's incredibly difficult to detect because all the transaction details look perfect. You can get the full picture by exploring the Merchant Risk Council's global fraud report.
Comparing Modern Fraud Detection Techniques
Choosing the right mix of fraud detection tools can be daunting. Each technique has its own strengths and weaknesses. The table below breaks down the most common methods to help you understand where each one fits into a modern fraud prevention strategy.
TechniqueHow It WorksBest ForLimitationsRule-Based SystemsUses a predefined set of "if-then" statements to flag or block transactions based on specific criteria.Catching known, obvious fraud patterns quickly. Setting firm, non-negotiable business policies.Rigid and static. Can be easily bypassed by savvy fraudsters. Can create a high number of false positives.Machine LearningAnalyzes massive datasets to learn complex, subtle patterns associated with fraudulent and legitimate behavior.Identifying new and emerging fraud tactics. Reducing false positives by understanding context. Scoring risk with high precision.Requires large amounts of clean data to train effectively. The "black box" nature can make decisions hard to interpret.Anomaly DetectionEstablishes a baseline of "normal" behavior for a customer and flags any activity that significantly deviates from it.Spotting account takeover (ATO) and unusual spending patterns on established customer accounts.Less effective for new customers who have no established behavioral history. Can be triggered by legitimate but unusual life events.Device FingerprintingCreates a unique identifier for a user's device (computer, phone) based on its hardware and software configuration.Uncovering fraud rings where one person uses multiple stolen identities from a single device.Can be spoofed by sophisticated fraudsters. Privacy regulations can limit the data available for fingerprinting.
Ultimately, the most resilient fraud systems don't rely on a single approach. They combine the speed of rules, the intelligence of machine learning, and the observational power of behavioral analysis. This layered approach is what allows you to confidently accept good customers while putting up a formidable defense against fraudulent activity.
How to Integrate Fraud Detection Into Your Payments
It’s one thing to know the theory behind fraud detection, but putting it into practice is what actually protects your revenue. A modern, effective setup is all about a clean, API-driven architecture that runs a real-time risk analysis on every transaction. This lets you make instant, data-backed decisions without adding friction to your checkout process.
The flow itself is surprisingly direct. When a customer hits the "Buy" button, your system instantly packages the key details of that transaction. It fires them off to a dedicated fraud detection API, which, in milliseconds, returns a risk score. With that score in hand, you can automatically decide whether to approve, reject, or flag the payment for a quick manual review.
This isn't a single check. It's a layered process that combines everything from simple rules to sophisticated machine learning to build a complete picture of the risk involved.
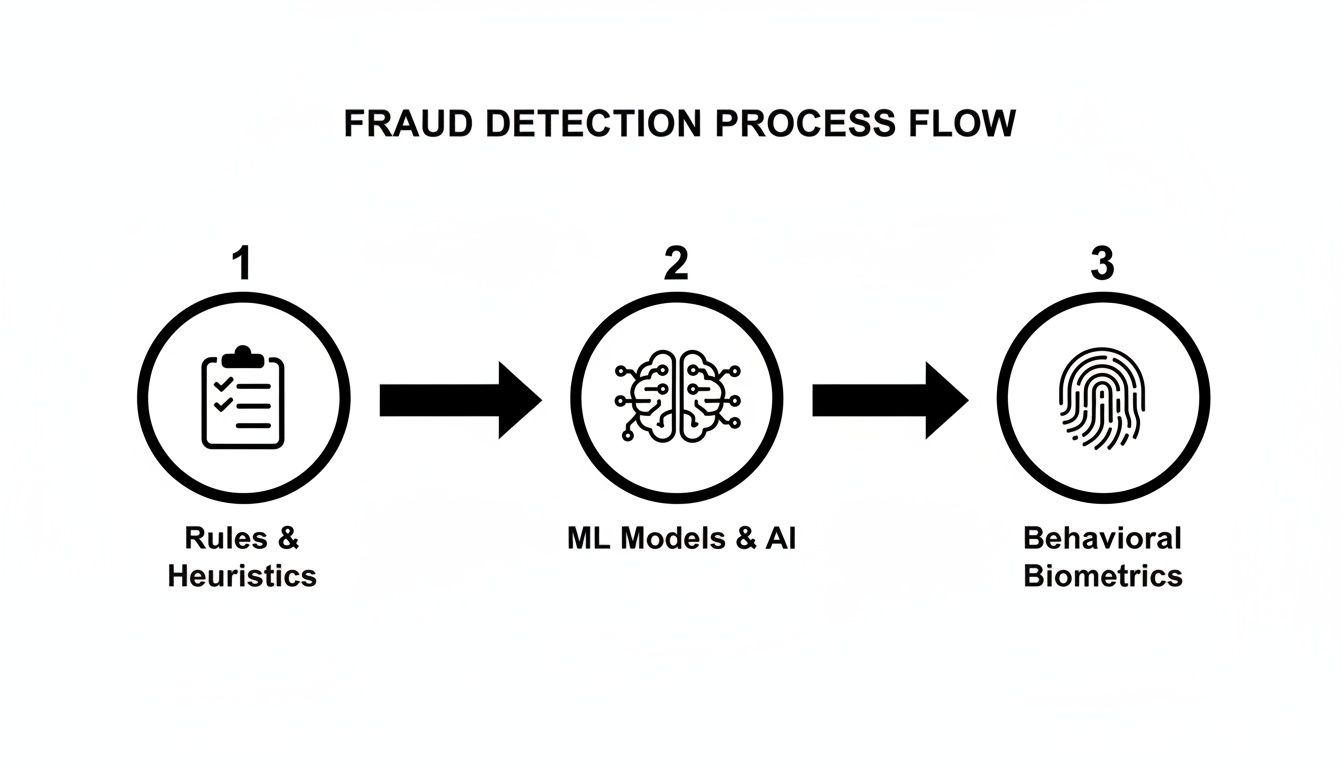
As you can see, different techniques work together as a defense-in-depth system. It starts with the basics, like static rules, then moves on to intelligent machine learning models, and can even incorporate things like device fingerprinting. Each step catches different kinds of fraud, making the system tough for attackers to beat.
Choosing an API-First Approach
Let's be realistic: for most businesses, building a fraud detection engine from scratch is a massive distraction. It demands specialized data science talent, huge datasets to train your models, and constant upkeep to stay ahead of new threats. Frankly, it’s a full-time job. This is where leaning on a payment solution with built-in protection makes all the difference.
Going with an API-first approach means you get access to advanced fraud detection without the operational headache. You're essentially plugging into a service that has already done the hard work, freeing you up to focus on your actual product and customers.
A huge advantage of an API-based architecture is how it scales. As your business grows and transaction volume climbs, the fraud system scales right along with it. You get consistent protection without ever having to re-engineer your backend. It's enterprise-grade security delivered with the simplicity of an API call.
This is exactly the thinking behind a platform like Suby. It offers a straightforward, powerful API that lets businesses accept global card payments, with all payouts settled directly in USDC. Critically, high-end payment fraud detection is baked into its core, so every transaction is protected from the get-go. You get the benefit of a best-in-class security layer without any of the complexity.
How a Modern Payment API Works
Integrating a solution like Suby is designed to be incredibly flexible. Merchants can spin up shareable paylinks for quick invoicing, embed a conversion-optimized checkout on their site, or build entirely custom flows with the API and webhooks. The platform handles both one-time sales and recurring subscriptions out of the box.
And while your customers get the flexibility to pay with Visa, Mastercard, or even various crypto assets, you get the stability of receiving all your revenue in USDC.
This unified model means all the tough security work, including PCI compliance, is handled for you. If you want to dive deeper into those requirements, our guide on what PCI DSS compliance entails is a great place to start. By integrating a single solution, you're not just simplifying payments, you're offloading a huge chunk of your security and compliance burden. That means you can operate with a whole lot more peace of mind.
Finding the Right Balance for Your Business
Getting the tech right for fraud detection is a huge win, but it’s really only half the job. The other, arguably trickier, half involves people and strategy. You're constantly walking a tightrope between locking down your business and making sure your legitimate customers don't get caught in the crossfire.
Lean too hard on security, and you’ll inevitably block good customers, a phenomenon known as a false positive. That’s not just lost revenue; it’s a soured customer relationship. But if you’re too relaxed, you're practically inviting fraudsters to take advantage. The sweet spot is found by constantly watching your metrics and being willing to adjust your rules on the fly.
Setting Your Risk Thresholds
Deciding what level of risk is "too risky" feels more like an art than a science, and every business will have a different answer. A risk threshold is simply the score where your system decides to either block a payment or flag it for a human to look at.
If you set this cutoff too low, you'll be swimming in false positives, and your team will spend their days reviewing perfectly good orders. A better way to think about it is with a tiered system, not a single hard line.
- Low-Risk Scores: These transactions should fly through. Auto-approve them for a fast, smooth checkout experience.
- High-Risk Scores: These are the obvious red flags. Auto-decline them immediately to stop fraud in its tracks.
- Mid-Range Scores: This is the gray area. Send these transactions to a manual review queue where a trained team member can make the final call.
This layered approach stops your system from being a blunt instrument. It lets you capture legitimate sales that might look a little unusual while still maintaining a strong defense.
The Power of a Unified Platform
Trying to manage payments, chargeback disputes, manual reviews, and customer support across a patchwork of different tools is a recipe for disaster. It scatters your data, making it nearly impossible to see the full story of a customer's journey. This is a massive headache, especially for companies expanding globally or those with active online communities.
A single, unified platform brings all of this under one roof. For instance, our API doesn't just let you accept card payments with USDC payouts; it also gives you the tools to manage the entire process. Security is baked right in—Suby works with a PCI-DSS Level 1–certified processing partner and includes features like strong customer authentication, two-factor authentication, dispute management, and zero-fee refunds. You can get the full rundown on how Suby's security features are designed.
When your payments and security operations are in one place, your team can make smarter decisions, faster. They aren't toggling between five different dashboards to piece together what happened. All the context they need is right there.
This is a game-changer for anyone running a subscription business or a paid community. Our native integrations for Discord and Telegram, for example, tie payment processing directly to access management. It creates a completely seamless experience for you and your members, so you can focus on growing your community, knowing the platform is handling the tough stuff in the background.
Common Questions About Payment Fraud
As you get deeper into fraud detection, some common questions tend to surface. Let's walk through the answers to a few of the most frequent ones we hear from teams just like yours.
What Is The Difference Between Fraud Detection and Fraud Prevention?
It's a common point of confusion, but the two serve very different roles. Think of fraud prevention as the first line of defense, it’s the fence and the locked gate around your property. These are tools like Strong Customer Authentication (SCA) or basic address verification (AVS) that stop the most obvious, low-effort attacks before they can even make a dent.
Fraud detection, however, is your highly-trained security team actively monitoring everything inside the gate. It's what catches the sophisticated fraudster who found a way to climb the fence. Detection systems analyze transaction data in real time to spot subtle, suspicious patterns that prevention tools would miss. You absolutely need both: prevention to block the easy stuff and advanced detection to outsmart the determined criminals.
How Can I Reduce False Positives In My System?
This is the million-dollar question. False positives, when you block a legitimate customer by mistake, are incredibly frustrating and directly hurt your bottom line. The best place to start is by digging into your declined transactions. Are you seeing a pattern? Maybe good customers from a specific country or those using a particular type of prepaid card are getting flagged too often.
Once you spot a trend, you can fine-tune your rules or feed that data back into your machine learning models to make them smarter. It’s also wise to set up a manual review queue for transactions that are "on the fence." This allows a human to give the final say, saving sales that an automated system might have rejected. Honestly, working with a payment platform that sees a massive volume of global transactions is a huge advantage here, as its models have learned to recognize a much wider range of normal customer behavior.
A well-tuned system finds the balance between security and customer experience. The goal is to stop fraudsters without creating unnecessary friction for your real customers, maximizing both safety and sales.
Does Accepting Crypto Payments Increase My Fraud Risk?
The risk profile definitely changes, but it's not necessarily higher, it's just different. With a pure crypto-to-crypto transaction, the irreversible nature of the blockchain means traditional chargeback fraud is off the table. The risks shift to things like wallet takeovers or phishing attacks on the customer's end.
However, when you use a managed service, this is handled for you. For example, our platform lets customers pay with cards or crypto, but your business gets paid out in stable USDC every time. For your card-paying customers, the risk is still chargeback fraud, which is exactly why you need a robust detection system. A unified platform like ours is designed to manage these distinct risks under one roof, so you can securely accept all the ways your customers want to pay.
Ready to protect your revenue with advanced fraud detection built-in? Suby provides a simple API that allows any business to accept payments by card or crypto, with all payouts settled in USDC. Get started today at Suby.fi.