At its simplest, payment fraud is when a criminal uses stolen information to make an unauthorized purchase or transfer funds from your business. But it's rarely that straightforward. We're not just talking about someone finding a lost credit card anymore; we're dealing with sophisticated schemes designed to exploit the very systems that power online commerce.
Understanding the Modern Landscape of Payment Fraud

Let's be clear: if you take payments online, you are a target. This isn't a problem reserved for big-box retailers. It hits everyone, from SaaS companies and e-commerce shops to creators monetizing communities on Discord or Telegram. As more of the world moves online, so do the opportunities for bad actors to find and exploit weak spots.
The numbers are genuinely alarming. Global losses from online payment fraud are expected to hit a staggering $362 billion by 2028, with card-not-present (CNP) transactions being the primary battleground. It’s a massive drain on the global economy, directly impacting revenue, customer trust, and brand reputation for businesses of all sizes.
Why Payment Fraud Is an Urgent Business Problem
At its core, every fraudulent transaction is a direct hit to your revenue. It often ends in a chargeback, which means you lose the sale, the product, and get slapped with extra fees. For any business that depends on a smooth payment gateway for its income, these costs can quickly spiral out of control.
But the damage doesn't stop there. Fighting fraud eats up time and money that you should be investing in growth. It can also create a clunky experience for your legitimate customers, forcing them through extra verification steps that might just convince them to abandon their cart altogether.
For any online business, a solid fraud prevention strategy is not just a security measure; it's a fundamental part of maintaining a healthy cash flow and building a sustainable company. It protects your bottom line and ensures your legitimate customers have a seamless experience.
The Most Common Fraud Schemes at a Glance
To build a strong defense, you first need to know what you're up against. Fraudsters have a diverse toolkit, and understanding their favorite methods is the first step toward spotting the red flags. Getting a clear picture of these schemes helps you put the right protective measures in place.
Here’s a quick overview of the most prevalent forms of payment fraud that online businesses face.
Quick Guide to Common Payment Fraud Types
This table provides a quick overview of the most prevalent forms of payment fraud that online businesses face.
Think of this as your field guide to the enemy. In the sections that follow, we'll dive deeper into each of these threats, giving you the practical knowledge you need to build an effective defense.
The Five Most Common Types of Payment Fraud
To stop fraud, you first have to know what you’re up against. Fraudsters aren't using a one-size-fits-all approach; they have a whole toolkit of schemes, each with its own tell-tale signs and consequences. Getting familiar with these tactics is the first real step toward protecting your business, whether you're running a SaaS platform or building a paid community.
Let's walk through the five types of payment fraud you're most likely to encounter. We'll look at how they work, who gets hit the hardest, and what they actually cost you.
Card-Not-Present Fraud
This is the bread and butter of online crime. Card-Not-Present (CNP) fraud is exactly what it sounds like: a crook uses stolen credit or debit card details to buy something without having the physical card. They get this information from data breaches, phishing emails, or malware that scrapes card numbers right from a customer's computer.
Think about it from their perspective. A fraudster buys a fresh list of stolen card numbers on the dark web. They can then immediately turn around and use that info to buy digital goods from a merchant like you, maybe a software license or access to an online course. Since you can't physically see the card, it's an easy target.
CNP fraud is a constant threat for any business that takes payments online. When a dispute arises, the burden of proving the transaction was legitimate almost always falls on you, the merchant, making it incredibly tough to win and recover your money.
The damage is straightforward: lost sales, painful chargeback fees, and a hit to your business's reputation. It's a game of cat and mouse that forces you to treat every single online transaction with a healthy dose of suspicion.
Chargeback Fraud or Friendly Fraud
Sometimes, the call is coming from inside the house. Chargeback fraud, often called "friendly fraud," is when a real customer buys something with their own card and then disputes the charge with their bank. They’ll claim they never authorized it, the item never arrived, or it wasn't what they expected.
It’s the digital version of a "dine-and-dash." Imagine someone subscribes to your service, uses it for a few weeks, and then calls their bank to say they never signed up. Just like that, they get the service for free. You, on the other hand, are out the revenue, the product, and now have to pay a hefty chargeback fee to your payment processor.
It’s not always malicious. Sometimes it's just a case of buyer's remorse or someone not understanding a return policy. But as you dig deeper into specific categories like friendly fraud, you'll find the financial hit is just as real, regardless of the customer's intent.
Account Takeover Fraud
Account Takeover (ATO) fraud is a digital home invasion. A criminal gets their hands on a legitimate user's login credentials and breaks into their account on your platform. From there, they can make purchases with saved payment methods, scrape personal data, or even change the password to lock the real user out. This is a massive headache for any business built on user accounts, from SaaS and e-commerce to communities on Discord or Telegram.
How do they get in?
- Credential Stuffing: They take huge lists of stolen usernames and passwords from other data breaches and test them on your site, hoping for a match.
- Phishing: They send clever, deceptive emails or set up fake login pages to trick your users into handing over their credentials.
- Brute-Force Attacks: An automated script tries millions of password combinations on a single account until it gets in.
Once they're inside, the damage goes beyond just one fraudulent transaction, it can shatter your customer's trust in your brand.
Synthetic Identity Fraud
This one is the long con. With synthetic identity fraud, criminals don't steal a person's entire identity. Instead, they act like Frankenstein, stitching together real and fake information to create a brand new, "synthetic" person. For example, they might pair a real, stolen Social Security Number with a made-up name and address.
With this new identity, they patiently build a credit history. They'll apply for a credit card, take out a small loan, and make all their payments on time. Once they've established a respectable credit score, they "bust out" by maxing out every credit card and loan at once with zero intention of ever paying it back. This is especially devastating for financial services and any business extending lines of credit.
Refund Abuse
Finally, there's refund abuse, where people exploit your generosity. While not always a crime in the legal sense, it's a direct drain on your revenue. It can be as simple as someone claiming their package never arrived to get a free replacement and a refund, or returning a heavily used item for a full refund.
For anyone selling digital goods or subscriptions, this is a particularly nasty problem. A user could join your paid community, download every piece of exclusive content, and then demand a refund under your "no questions asked" policy. They get all your valuable work for free, which not only costs you money but also cheapens the product for your honest, paying customers.
This isn't a small problem, either. Consumer fraud losses skyrocketed 25% year-over-year, hitting over $12.5 billion in 2024. As these trends continue to climb, businesses are being forced to completely rethink their policies and defenses. You can learn more about these escalating fraud statistics and their impact on businesses to see just how serious the situation has become.
How to Detect and Analyze Fraud Signals
Knowing the names of different fraud types is one thing; learning to spot them in real time is where the real work begins. Every single transaction leaves behind a trail of digital breadcrumbs. For a fraud fighter, these breadcrumbs are clues, signals that help you tell a genuine customer from someone trying to game your system.
To do this effectively, you need to look at two kinds of signals: technical and behavioral. Think of technical signals as the hard data, the "what" and "where" of a transaction, like an IP address or device ID. Behavioral signals are all about the "how," the user's actions and patterns during checkout. By combining both, you build a far more robust defense.
The infographic below shows the main fraud categories you'll be looking for signs of, from Card-Not-Present (CNP) fraud to Account Takeovers (ATO).
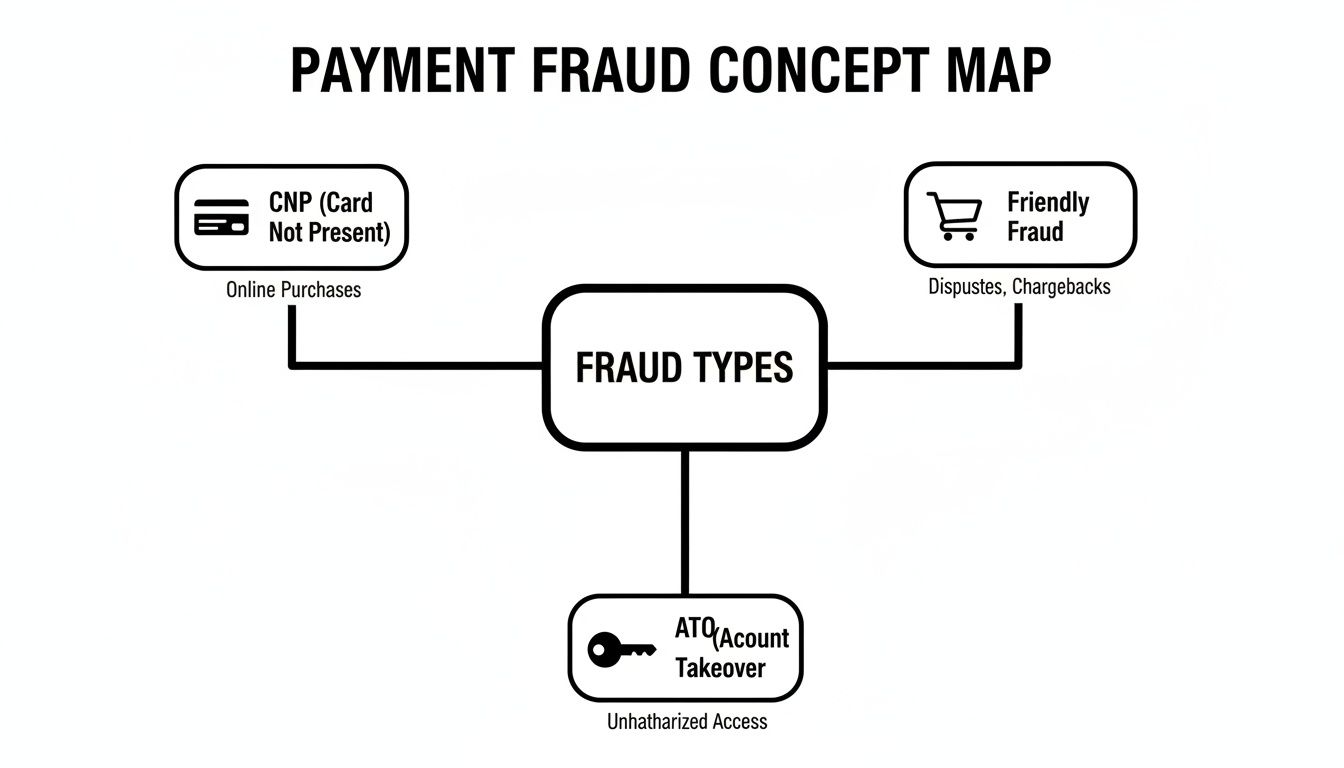
As you can see, schemes like CNP fraud and account takeovers are distinct problems, and each requires you to look for its own unique set of signals.
Reading the Technical Tea Leaves
Technical signals give you an objective, behind-the-scenes look at a transaction. Your payment system can scan these data points automatically, flagging suspicious activity long before a human ever gets involved. They're your first line of defense.
Here are a few of the most powerful technical signals we see in the field:
- IP Address Mismatches: This is a classic. Does the customer’s IP address place them in a country that's different from their billing address? A credit card issued in Germany being used from an IP in Nigeria is an immediate and major red flag.
- Proxy or VPN Usage: Fraudsters love using proxies and VPNs to mask their location. While plenty of legitimate customers use VPNs for privacy, their presence should still raise a transaction's risk score, especially if other warning signs are present.
- Device Fingerprinting: Every phone and computer has a unique digital "fingerprint." If you see a dozen orders from different "customers" all originating from the same device, you've likely caught a single fraudster burning through a list of stolen cards.
These signals are the building blocks of a risk profile for every transaction. For developers, a great way to get a feel for this is to simulate different scenarios. Our guide on using test cards for Stripe is a perfect resource for safely testing your detection logic without risking real money.
Uncovering Behavioral Red Flags
On the flip side, you have behavioral signals. These are all about context and how a person interacts with your site. A legitimate customer in a buying mood acts very differently from a criminal in a hurry, and those differences are your clues.
Keep an eye out for these common behavioral patterns:
- Rapid, Repeated Purchase Attempts: A fraudster with a list of stolen cards will often try them one after another. Seeing multiple failed payments from the same user within minutes is a tell-tale sign of card testing.
- Mismatched Billing and Shipping Information: This can be tricky, as people often send gifts. But a mismatch should always trigger a second look, especially if the shipping address is a known high-risk area or a freight forwarding service.
- Small Test Purchases: Before making a big score, fraudsters often test a stolen card with a tiny purchase just to see if it's active. That $1.00 charge could be the prelude to a $1,000 fraudulent order.
It's crucial to remember that no single signal is a silver bullet. The real key is to look for a combination of signals. A customer using a VPN might just value their privacy. But a customer using a VPN with a mismatched IP address who tries five different cards in two minutes? That’s almost certainly fraud.
The threat is always evolving. Attack rates are skyrocketing in certain sectors, ticketing and reservations have seen an 85% year-over-year rise. Meanwhile, financial institutions and fintechs are weathering a 90% increase in attacks as fraudsters target weak spots like rewards programs. You can discover more insights about the evolution of payment fraud and see how these trends are hitting different industries.
Core Strategies for Your Fraud Prevention Playbook
Spotting the signals of fraud is a great first step, but actually stopping it? That takes a real game plan. This is your playbook for building a defense system with multiple layers, designed to protect your business from the ever-present threat of payment fraud.
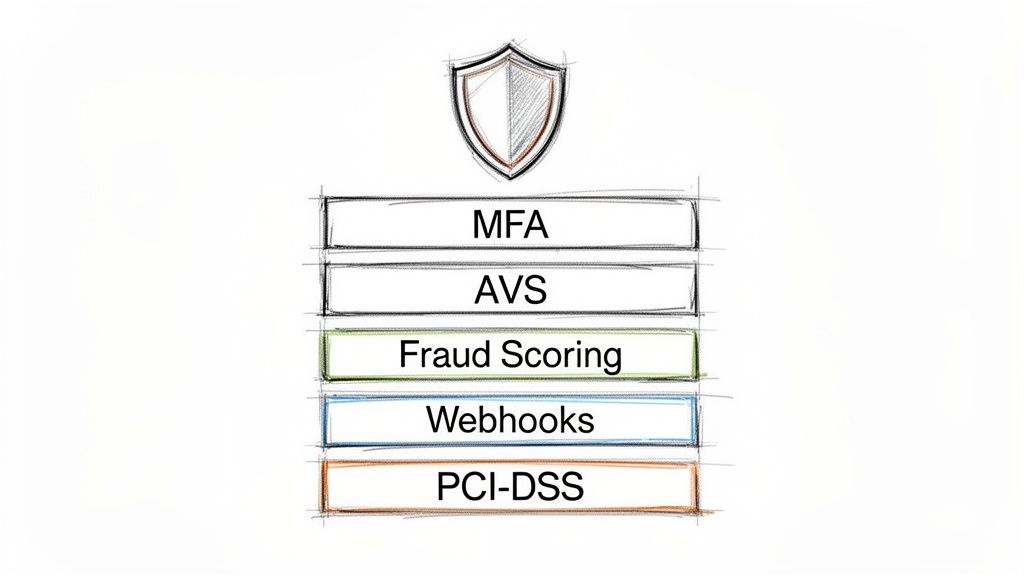
A truly strong defense isn't about finding a single magic bullet. It’s about creating layers of security that work in concert. This approach makes life incredibly difficult for criminals while keeping the checkout process smooth for your legitimate customers.
Start with Automated Fraud Scoring
The bedrock of any modern fraud prevention stack is an automated fraud scoring system. Think of it as a bouncer for your checkout page, instantly sizing up every transaction in real time. It looks at hundreds of data points, everything from the customer’s IP address and device to their purchase history.
Based on this analysis, the system assigns a simple risk score to each transaction. From there, you set the rules.
- Low-Risk Score: The transaction sails through automatically. No friction, happy customer.
- Medium-Risk Score: The transaction gets flagged. Maybe it needs a quick manual look-over or asks the customer for one extra piece of proof.
- High-Risk Score: The transaction is blocked on the spot.
This automated first pass is crucial. It stops the most blatant fraud attempts dead in their tracks without slowing down your good customers.
Add Essential Verification Layers
Beyond scoring, you need a few more checkpoints to confirm a buyer is who they claim to be. These verification tools add powerful, targeted layers to your defense.
One of the most effective is Multi-Factor Authentication (MFA). This is where you ask a customer for two or more forms of identification. A classic example is having them enter their password and then a temporary code sent to their phone. MFA is absolutely critical for stopping account takeover fraud, especially for SaaS businesses or creator communities with user logins.
Another simple but vital layer is the Address Verification System (AVS). This service just checks if the billing address provided matches the one the credit card company has on file. A mismatch isn’t always fraud, but it’s a big red flag, especially when combined with other suspicious signals.
By combining tools like MFA and AVS, you build a security net that catches a much wider range of fraudulent activity. You move from just reacting to fraud to proactively stopping it at the point of purchase.
Harness Real-Time Transaction Monitoring
Fraudsters are fast, which means your defenses have to be faster. Real-time transaction monitoring involves keeping a constant watch on payment activity as it happens, letting you spot patterns that an individual transaction review would miss.
For instance, real-time monitoring can alert you if:
- A single IP address tries to use dozens of different credit cards in just a few minutes.
- An account that’s been inactive for a year suddenly tries to make a huge purchase.
- A user quickly changes their shipping address and phone number right before hitting "buy."
This constant vigilance is key. And when fraud does slip through, remember that having effective chargeback representment strategies is also a critical part of the playbook for recovering lost revenue.
Empower Developers with Webhooks
For the developers on your team building out custom payment flows, webhooks are a true game-changer. A webhook is just an automated message sent from one app to another when a specific event occurs. For payments, they act as instant alerts for critical fraud events.
Imagine your payment system flags a high-risk transaction. Instead of you finding out in a report hours later, a webhook can instantly ping your internal systems. This can trigger a custom, automated workflow, like temporarily locking the user's account, canceling the order, or alerting your support team to investigate immediately.
By using a payment API that supports webhooks, developers can build a highly responsive and automated fraud prevention system tailored to your exact business needs. This is a must-have for anyone who needs to react to threats in real time, from a big e-commerce store to a creator managing subscriptions on Discord or Telegram. At Suby, our API does exactly this, enabling businesses to accept card payments while settling in USDC and building these kinds of robust, custom workflows.
Building a Modern Fraud Mitigation Stack
Knowing the theory is one thing, but putting it all together into a real-world defense is the real challenge. A modern fraud mitigation stack isn't just a random assortment of tools. Think of it as a coordinated system, with each layer working together to protect your revenue without getting in the way of legitimate customers.
This is exactly why your payment layer is so critical. Instead of trying to build an entire security apparatus from scratch, you can choose a payment provider that already has these defenses baked in. That frees you up to focus on what you do best, whether that's shipping software or building a creator community.
A Secure Foundation for Global Payments
Every solid fraud prevention strategy starts with a secure payment processor. If you accept credit cards online, this isn't negotiable. You need to work with partners who meet the absolute highest industry standards for handling sensitive cardholder data.
At Suby, we provide a global payment layer that lets any business accept payments by card or crypto. When your customers pay with a card, you receive the settlement directly in USDC. This entire process is anchored by our partnership with a PCI-DSS Level 1-certified provider, the most rigorous certification out there.
This secure foundation means raw card data is handled in a fully compliant environment, which dramatically reduces your own risk and the headache of PCI compliance. If you're new to the topic, it’s worth taking a moment to learn more about what PCI-DSS compliance entails and why it's a non-negotiable part of payment security.
Integrating Compliance and Authentication
A modern payment stack does more than just move money; it must also handle crucial authentication rules. For example, regulations like Europe's Strong Customer Authentication (SCA) are becoming the norm worldwide. These rules require extra verification for many online purchases to prove the buyer is the legitimate cardholder.
A payment provider that natively supports SCA ensures you remain compliant in key markets and adds a powerful layer of fraud prevention right at checkout. It helps verify that the person making the purchase is who they say they are.
Suby is built to manage these requirements from the ground up, so you can sell to an international audience without hitting compliance walls. By integrating this from the start, you can offer a checkout experience that customers everywhere trust.
Building Custom Workflows with an API
For developers and businesses with unique needs, a one-size-fits-all approach to fraud simply doesn't work. The rules that are too generic will miss sophisticated attacks, while rules that are too strict end up blocking good customers. A flexible API is what gives you the power to build a truly custom defense.
Suby’s API and webhooks are designed to give developers that fine-grained control. Webhooks, in particular, are incredibly powerful. They send you real-time notifications about payment events, which lets you build automated workflows that respond to suspicious activity the moment it happens.
For instance, you could use a webhook to:
- Fire off an alert to a Slack channel whenever a large transaction comes from a high-risk country.
- Put an order on hold for manual review if a customer’s billing and shipping addresses are a mismatch.
- Automatically flag an account for closer monitoring after it triggers several failed payment attempts in a row.
This level of control allows you to shape your fraud logic around the specific risks your business model faces. For creators using our native integrations with Discord and Telegram, these secure payment rails protect their subscriptions and paid communities, making sure their revenue is both predictable and safe.
Creating Your Incident Response Plan
Even with the best defenses in place, fraud is a reality of doing business online. It’s not a question of if it will happen, but when. When you spot that first suspicious transaction, the last thing you want is your team scrambling in a panic.
That’s where a solid incident response plan comes in. Think of it as your emergency playbook. It provides clear, pre-defined steps that turn a potential crisis into a manageable process. This is especially true for businesses built on recurring revenue, like creators with paid Discord or Telegram communities or SaaS platforms serving a global user base.
What to Do the Moment You Suspect Fraud
Those first few minutes after detecting a potential fraud event are everything. Acting quickly and decisively can stop the bleeding and give you the upper hand for any disputes that follow. Your operations manager or support lead should be trained to jump into action immediately.
The following checklist outlines the critical first steps to take as soon as a fraudulent transaction is detected. Having this process documented ensures a consistent and effective response every single time.
Incident Response Checklist
Following these steps systematically not only helps you fight a single fraudulent transaction but also gives you invaluable data. You can then use these insights to fine-tune your fraud prevention rules and make your entire system smarter for the future.
Handling Chargebacks and Customer Communication
Once you’ve contained the immediate threat, the focus shifts to managing the chargeback and handling communication. When you submit a dispute, you’re not just sending paperwork; you’re building a case. Be professional, stick to the facts, and provide every piece of evidence you collected.
Communicating with the legitimate customer, especially in an account takeover scenario, is just as important. Proactively reach out to them. Let them know what happened, explain the steps you’ve taken to secure their account, and guide them on what to do next.
Believe it or not, a negative event like this can be a moment to build trust. By handling a fraud incident with transparency and professionalism, you show customers you're serious about protecting them. This reinforces that your business is reliable, which can strengthen loyalty in the long run. We help businesses achieve this by providing secure payment rails that let them handle card transactions while getting settled in USDC.
Your Top Payment Fraud Questions, Answered
When you're building out your fraud defenses, a lot of questions come up. It's easy to get overwhelmed. Let's cut through the noise and tackle some of the most common concerns we hear from businesses.
How Much Should I Spend on Fraud Prevention Tools?
There’s no one-size-fits-all budget, but there’s a smart way to figure out your number. Start by looking at what you're currently losing.
What’s your chargeback rate? If a fraud prevention tool costs less than what you're losing to chargebacks and fraudulent orders each month, then it's a no-brainer, the tool will pay for itself.
Before you spend a dime, make sure you've enabled the basic, often free, risk tools that come with your payment processor. This includes things like Address Verification System (AVS) checks. As your business scales, you can layer on more powerful solutions like a dedicated fraud scoring system. The goal is simple: make sure every dollar you spend on prevention saves you more than a dollar in losses.
Will Tighter Security Hurt My Sales?
This is a huge and completely valid concern. Nobody wants to add so much friction at checkout that legitimate customers give up and leave. The trick isn't to build a fortress, but to apply security intelligently.
Think of it like a security guard at an event. They don't give everyone a full pat-down. They greet most people with a smile and only pull someone aside for a closer look if they seem suspicious. A modern fraud stack works the same way.
Good fraud prevention allows legitimate customers to sail right through. It only adds extra steps, like an SMS code, when a transaction shows multiple red flags. This keeps your checkout smooth for the vast majority of your customers while stopping criminals in their tracks.
Can I Stop All Fraud?
Honestly? No. If a fraudster is determined enough and has deep pockets, they can sometimes find a way through even the most sophisticated defenses.
The real goal isn't to hit zero fraud, it's to make your business a much harder, less profitable target than the next one. By implementing a layered defense, you dramatically increase the effort and cost for criminals to attack you. Most will simply give up and move on to easier targets. Your aim is to reduce fraud to a small, predictable, and manageable business cost.
At Suby, we build a secure payment layer that makes global commerce simple. Our API lets any business accept card payments and receive settlements in USDC. We even have native integrations for Discord and Telegram, which is perfect for creators and communities looking to manage subscriptions. To see how we can help protect your revenue, check us out at https://suby.fi.