E-commerce payment fraud is projected to rise from $44.3 billion in global losses in 2024 to $107 billion by 2029, a 141% increase according to Sift’s analysis of payment fraud trends. That number changes how founders should think about fraud. This isn't a back-office nuisance or a narrow card-operations issue. It's a growth constraint.
For online businesses, payment fraud sits at the intersection of checkout conversion, customer trust, support workload, and cash-flow predictability. Developers see it in API abuse and suspicious traffic patterns. Founders see it in rising dispute volume, blocked payments, and time lost to manual review. Community operators see it when bad actors buy access with stolen cards, drain perks, and disappear before the dispute lands.
The hard part is that fraud doesn't come from a single weak point. It shows up in card checkouts, account access, refund flows, and internal approval processes. If you sell internationally, traditional banking rails can add more delay, more reconciliation overhead, and more room for fraud-related confusion. That’s one reason many internet-native businesses are rethinking payment architecture. An API that lets customers pay by card while the business receives USDC can reduce some of the operational friction that older settlement flows tend to amplify.
Table of Contents
- The Growing Challenge of Payment Fraud
- A practical comparison
- Why friendly fraud is hard to handle well
The Growing Challenge of Payment Fraud
Payment fraud is now a core operating risk for any business that accepts money online. For teams shipping products across borders through APIs, it shows up less as a single catastrophic event and more as a steady stream of expensive exceptions. Orders that need review. Accounts that look real until payout time. Refunds and reversals that consume support, finance, and risk hours.
The operational burden is what many founders underestimate. Fraud does not only hit authorization rates or direct loss. It creates reconciliation gaps, slows settlement, increases manual review queues, and makes it harder to tell the difference between customer error, abuse, and organized attacks. In practice, the payment team ends up running incident response inside the revenue engine.
Global businesses usually feel this pressure first. They sell into more regions, work across more issuers and banks, and support more payout paths. Every added market introduces new failure modes, from mismatched billing data to delayed settlement windows and weaker visibility across providers.
That matters even more for companies that collect funds one way and pay out another. A card checkout may be familiar to the customer, but if the business is settling through multiple banking partners, local currencies, and manual treasury steps, each fraud event becomes harder to contain. The payment method did not create all of the risk. The fragmentation around it made the investigation slower and the recovery messier.
A better setup reduces that drag. Many modern platforms now keep card acceptance on the front end while using stablecoin rails such as USDC for merchant settlement or contractor payouts on the back end. That does not stop stolen card use or account abuse. It does reduce some of the delay, opacity, and cross-border banking friction that often amplify losses after the fraud already happened.
I have seen this trade-off matter most in fast-growing businesses. Traditional bank rails can be familiar to finance teams, but they often add cutoff times, intermediary fees, return risk, and poor status visibility. Stablecoin payouts introduce their own controls requirement, including wallet verification, sanctions screening, and destination monitoring, but they can give operations teams faster finality and cleaner audit trails when set up well.
Email-driven fraud also rises as payment operations scale. Invoice changes, payout rerouting, and fake executive approvals can bypass checkout controls entirely, which is why teams handling vendor payments should treat Business Email Compromise (BEC) prevention as part of payment fraud defense, not a separate IT issue.
The practical rule is simple. Build fraud controls into payment architecture early. The companies that contain fraud best are usually not the ones with the longest rules list. They are the ones with fewer blind spots between checkout, identity, settlement, and payout.
Common Types of Payment Fraud Explained
Not all payment fraud works the same way. Teams get into trouble when they use one label for very different problems. A stolen card event, an account takeover, and a chargeback from a real customer need different controls and different evidence.
A practical comparison
The table below is the simplest way to separate the main categories.
| Fraud Type | What It Is | Primary Method |
|---|---|---|
| Card-not-present fraud | Unauthorized use of card details in an online transaction | Stolen card data used at checkout |
| Account takeover | A fraudster gets into a real user account and makes payments or redeems value | Stolen credentials, bot login attempts, session abuse |
| Crypto-related payment scams | Fraud involving deceptive wallet transfers, fake invoices, or manipulated destination details | Social engineering, address substitution, impersonation |
| Friendly fraud or chargeback abuse | A real customer disputes a valid transaction or exploits a policy after receiving value | Chargebacks, refund abuse, policy manipulation |
Card-not-present fraud is still the core problem for most digital merchants. The buyer isn't present, the merchant can't inspect a physical card, and fraud checks rely on digital evidence rather than face-to-face verification.
Account takeover is different. The payment itself may look valid because it comes from a real customer profile. Fraudsters log in, change details, buy access, use saved payment methods, or drain loyalty value. The danger is that support teams often read this as customer confusion rather than account compromise.
Why friendly fraud is hard to handle well
Friendly fraud causes some of the messiest internal debates because the customer often did receive something. That could be software access, a subscription renewal, community entry, or a digital good. The dispute arrives later, and teams start arguing over whether it was "real fraud" or "just support."
That framing is a mistake. The operational question isn't whether the team feels sympathetic. It's whether the merchant can prove authorization, delivery, and policy disclosure.
Dispute handling also has a people problem. Payment fraud discourse often neglects the psychological impact of victim-blaming on finance teams, even as 76% of organizations take over a month to detect and address discrepancies, as noted in this discussion of the AFP study and fraud culture. When a team defaults to blame, people hide mistakes, delay escalation, and preserve weak processes because nobody wants to be the person who "missed" the fraud.
Friendly fraud gets worse when support, finance, and engineering treat it as a customer-service annoyance instead of an evidence problem.
A practical response starts with classification:
- Criminal fraud: The payer was not the legitimate cardholder or account owner.
- First-party abuse: The buyer likely authorized the transaction but disputes it later.
- Policy abuse: The buyer uses refund rules, trial access, or incentives in a way your system didn't anticipate.
If your team also handles invoice approvals or manual transfer requests, it helps to train them on Business Email Compromise (BEC) prevention. BEC often sits outside the card workflow, but in practice it targets the same weak point, a human making a payment decision under pressure.
How Fraudsters Exploit Modern Payment Systems
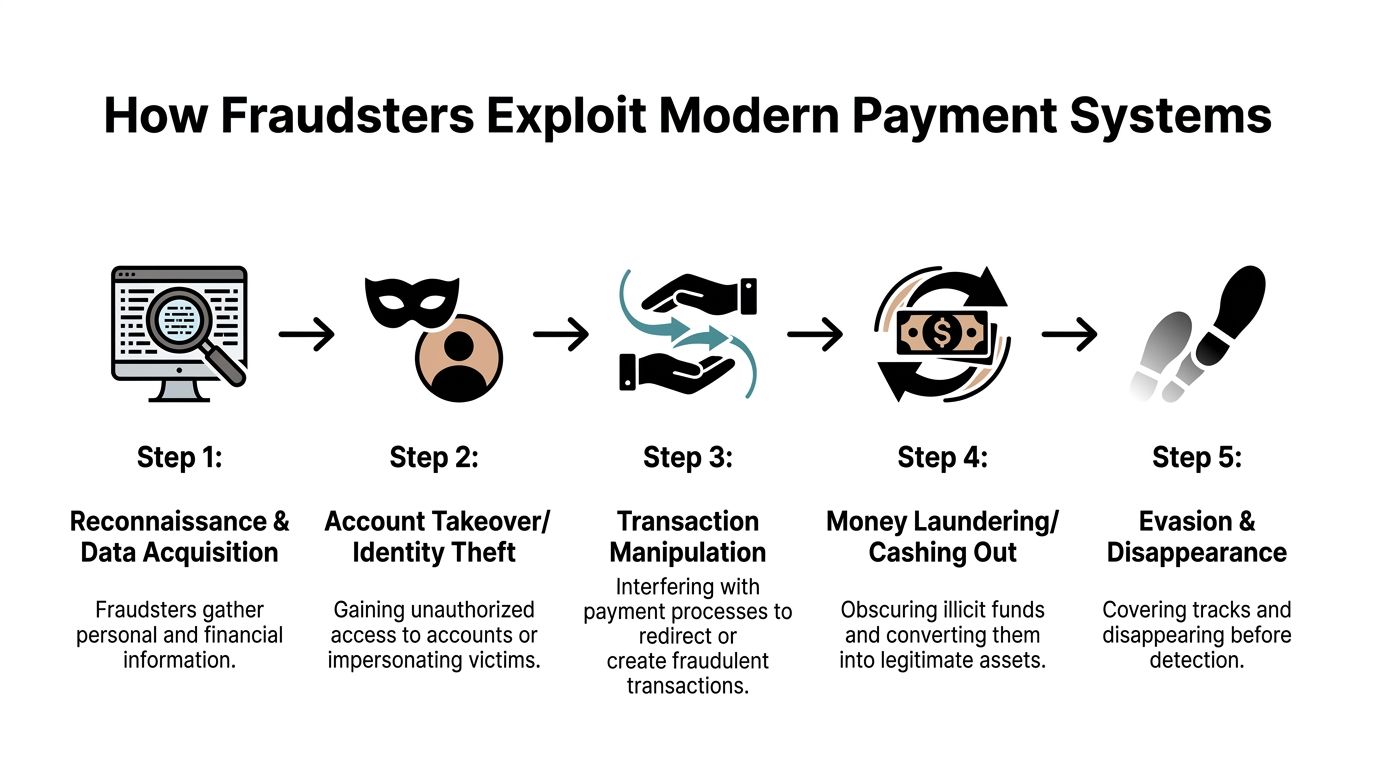
Fraudsters don't just steal payment data. They study how your checkout works, how your team approves exceptions, and where your logs are incomplete. The most effective attacks fit themselves into normal business traffic.
What a modern attack chain looks like
One of the clearest examples is Magecart. A retailer or digital merchant has a functioning checkout. A malicious script gets injected into the payment page. The transaction still appears to proceed normally, but the card data is copied as the customer enters it.
In 2025, industrialized Magecart attacks were responsible for over 10,500 active hacks, compromising more than 23 million transactions by injecting malicious JavaScript into payment pages to steal card data in real time, according to Recorded Future’s annual payment fraud intelligence report.
That matters because many teams assume server-side security is enough. It isn't. If the browser-side payment experience is compromised, attackers can capture data before it reaches secure processing systems.
A typical path looks like this:
- Reconnaissance: Attackers identify a vulnerable storefront, plugin, script dependency, or admin path.
- Injection: Malicious code is inserted into the checkout flow.
- Collection: Payment details are captured during live customer sessions.
- Monetization: Stolen data is used in online purchases or sold onward.
- Evasion: The attacker keeps the checkout functional to delay detection.
Why payment teams miss the early signs
The first signal often isn't a clear technical alarm. It might be a rise in customer complaints, a cluster of post-purchase fraud reports, or a pattern of disputes tied to a specific checkout path. Teams miss the pattern when ownership is fragmented. Engineering watches uptime, support watches tickets, finance watches disputes, and nobody has the full picture.
Social engineering follows the same logic. A finance employee receives an urgent request that appears to come from a legitimate executive or vendor. The attacker doesn't need to break the payment system directly. They just need to redirect trust.
If a payment event looks normal in one system but abnormal in the wider context, you need cross-functional review, not a local explanation.
The practical lesson is simple. Fraudsters exploit the handoffs. Browser to processor. Support to finance. Approval to settlement. That's where defenses need to be strongest.
Detecting Fraud with Key Signals and Data
Detection works best when you stop looking for a single "fraud flag" and start reading combinations of signals. One odd event usually means nothing. Several odd events in sequence often mean you should slow the transaction down.
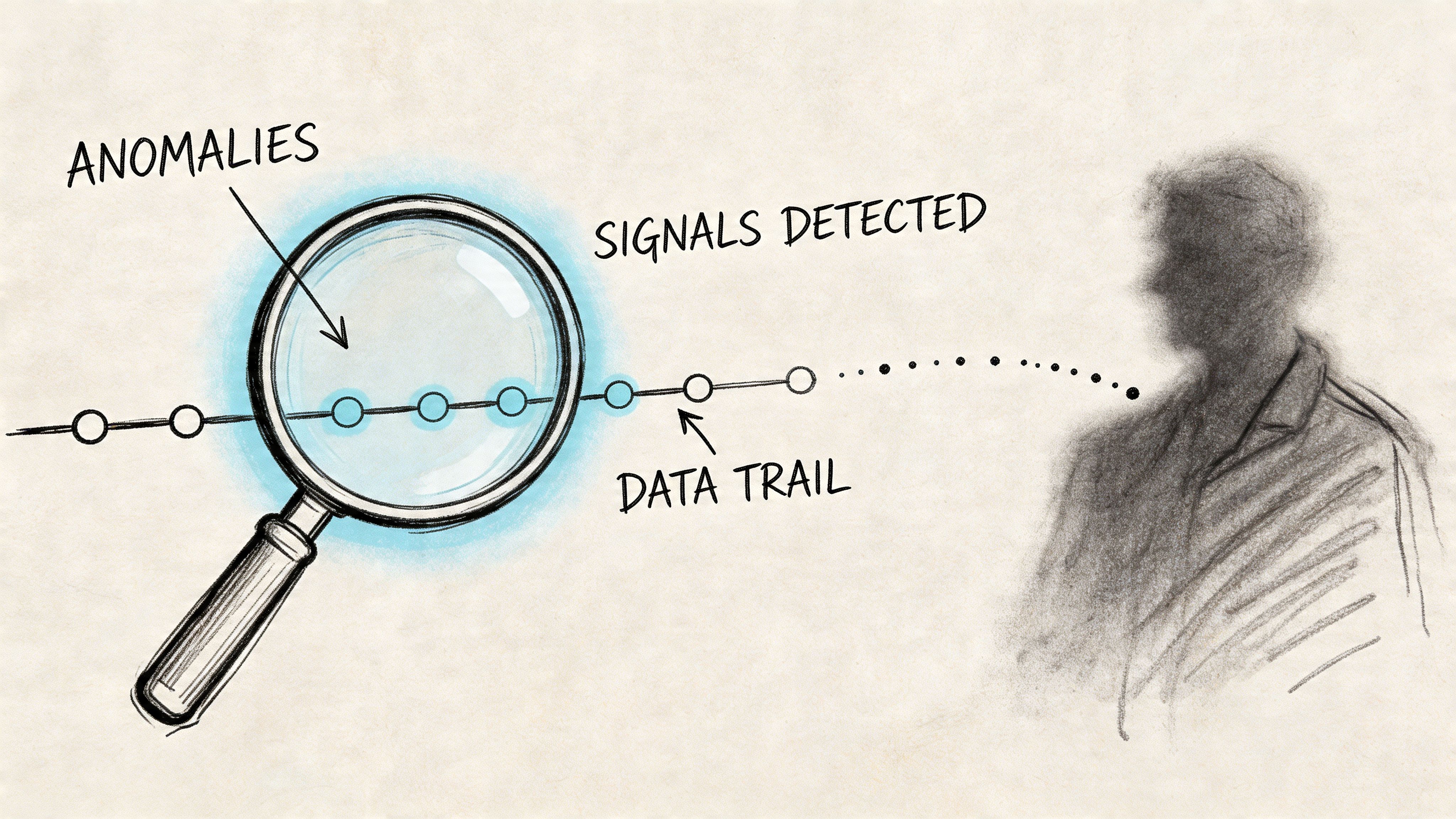
Signals that matter in real time
The strongest signals are usually boring. They come from consistency checks rather than dramatic anomalies.
- Device continuity: Has this account used this device before, or does the fingerprint suddenly change at purchase time?
- IP behavior: Does the location make sense for the customer, and is the connection coming through infrastructure associated with masking or rapid switching?
- Velocity: Is the same card, account, device, or user attempting too many actions too quickly?
- Session behavior: Did the user browse normally, or did they jump straight from login to payment, password reset, or reward redemption?
- Value mismatch: Does the order size, product type, or payout destination fit the account’s history?
These checks are most useful when they are tied to action. Low-risk events should pass with minimal friction. Mid-risk events should trigger stronger authentication or a review path. High-risk events should be declined or isolated.
For teams designing controls, a structured fraud risk assessment is a good way to map which signals matter most at checkout, during account access, and around refunds or subscription renewals.
Why rules alone stop working
Static rules help early on. Block impossible geographies. Flag repeated declines. Limit failed login bursts. But rules age badly because attackers test against them. Once they learn your thresholds, they adapt.
Predictive machine learning models can reduce false positives in fraud detection by 40-60% over rules-based engines by aggregating real-time signals like device intelligence, IP velocity, and proxy use into a single risk score, according to Mastercard’s coverage of Recorded Future’s fraud findings.
That trade-off matters. A system that catches fraud but blocks too many legitimate buyers hurts revenue and support load. A system that lets everything through keeps conversion high until disputes catch up.
This walkthrough on payment fraud detection is useful if you're mapping signals to practical review flows rather than treating detection as a black box.
A useful mental model is this:
Better fraud detection doesn't just find more bad transactions. It also lets more good transactions through with confidence.
For a quick visual explainer, this video gives a helpful overview of how modern payment fraud detection works in practice.
Building a Practical Prevention and Response Workflow
Most fraud programs fail because they rely on one control. A rule engine without good authentication. Strong authentication without webhook security. Good alerts without anyone assigned to act on them. The fix is operational layering.
Nearly a third of financial organizations now suffer direct fraud losses exceeding $1 million annually, up from just a quarter in 2024, with 60% of institutions reporting an increase in fraud attacks, according to Alloy’s 2025 State of Fraud Report. That pressure is why prevention has to be repeatable, not heroic.
Start with layered controls
A practical workflow usually includes these elements:
Risk scoring before authorization
Score the payment using device, identity, behavior, and transaction context. Don't force every buyer through the same path.Step-up authentication for uncertainty
When the signal is mixed, use strong customer authentication or 3D Secure rather than a blanket decline. That preserves good conversion while adding friction where it matters.Webhook verification and replay protection
Many teams secure checkout but ignore the event layer. If your payment webhooks aren't verified and deduplicated, an attacker may not need to beat your fraud model. They may target your internal state changes instead.Account protection around the payment flow
Login, password reset, payout changes, and plan upgrades all need controls. Payment fraud often starts before checkout.Reconciliation with ownership
Somebody needs to review exceptions daily. Not eventually. Not when finance closes the month.
Treat response like an operations function
The strongest teams write response playbooks for common scenarios. Not legal memos. Not abstract policy documents. Short operational guides.
A useful playbook should define:
- Who reviews high-risk orders
- What evidence gets retained automatically
- When to refund, block, or escalate
- How support should speak to customers during a fraud investigation
- How engineering should log payment, account, and webhook events
One option for businesses that want a unified payment setup is Suby, which provides an API that lets businesses accept payments by card or crypto, with customers able to pay by card while the business receives USDC, and it also offers native Discord and Telegram integrations for subscriptions, paid access, and online communities. In that kind of setup, the fraud controls around checkout still matter, but settlement and access management can be handled in a more consistent operational flow.
Operator habit: Review failed payments, chargebacks, refunds, and account changes together. Fraud rarely stays inside one dashboard.
Teams also underestimate training. Support agents should know what account takeover looks like. Developers should know why idempotency and webhook validation matter. Finance should know when an urgent payout request is a fraud signal rather than an exception to process quickly.
Managing Disputes and Chargebacks Effectively
A chargeback response shouldn't begin when the dispute arrives. By then, you're just assembling what your systems already captured, or failed to capture. Good dispute handling is mostly evidence discipline.
Build evidence before you need it
For card disputes, the merchant's job is to show a coherent record of the transaction. That usually means proving some combination of authorization, customer identity, service delivery, usage, and policy disclosure.
The strongest evidence sets tend to include:
- Transaction records: Authorization outcome, timestamps, and payment metadata
- Customer activity: Login history, account creation details, session continuity, or service usage
- Fulfillment proof: Access granted, subscription activated, download completed, or community entry provisioned
- Policy acceptance: Refund terms, billing disclosures, renewal messaging, and checkout consent
This guide to chargeback management is a useful reference if you're refining what to store at the moment of payment rather than trying to reconstruct it later.
Separate criminal fraud from customer abuse
The worst dispute responses are emotional. Merchants feel the customer is lying, support gets defensive, and the case file turns into argument instead of documentation.
Criminal fraud and first-party abuse need different treatment. If the cardholder clearly didn't authorize the transaction, focus on containment, account review, and pattern detection. If the customer likely did authorize it but now claims otherwise, focus on evidence quality and policy clarity.
USDC settlement doesn't change card-network dispute rules. A card payment can still be disputed through the normal process. What it can change is the merchant's operational picture after the transaction. If revenue is settled in USDC rather than moving through delayed cross-border banking flows, finance teams often have a cleaner view of what was received, when it was received, and how to reconcile activity while the dispute runs its course.
The goal in a dispute isn't to "win the argument." It's to present a clean factual timeline.
That mindset matters internally too. Teams handle disputes better when they stop treating them as isolated customer conflicts and start treating them as feedback on checkout clarity, evidence capture, and fraud controls.
Turn Your Payment System into a Strategic Defense
Payment fraud isn't just a security issue. It's an architecture issue. The controls you choose at checkout, the evidence you retain, the way you handle authentication, and the rails you use for settlement all shape how exposed your business is when something goes wrong.
A strong setup does a few things well. It identifies different fraud types instead of lumping them together. It reads behavioral and technical signals in real time. It applies layered controls rather than one blunt rule. It handles disputes with records, not guesswork.
For global online businesses, payment design also affects operational resilience. If buyers can pay with familiar methods like cards while the business receives USDC, you keep the front-end experience simple and reduce some of the settlement friction that traditional bank-dependent flows add behind the scenes. That matters for reconciliation, cross-border operations, and response speed.
If you're reviewing your stack, it's also worth understanding the basics of PCI DSS compliance, because secure payment handling starts with the foundation, not the fraud model layered on top.
If you're building a global checkout, subscription flow, or paid community and want a simpler payment architecture, Suby provides an API that lets any business accept payments by card or crypto, while businesses receive USDC. It also includes native Discord and Telegram integrations for subscriptions, paid access, and community monetization. Users pay with cards, businesses receive USDC.