You’re probably asking this because payment processing sits too close to the core of your business to get wrong. If you’re launching a SaaS product, opening a cross-border store, or setting up subscriptions for a community, the processor you choose won’t just move money. It will hold customer card data, screen transactions, handle disputes, and in some cases decide whether your payouts keep flowing.
That’s why “is stripe safe” isn’t a casual question. It’s really two questions. First, is Stripe technically secure enough to trust with customer payment data? Second, is it operationally safe for your business, meaning you can access your money when you need it?
Those are not the same thing.
A processor can be excellent at encryption and still create stress for merchants through reserves, reviews, or payout delays. Businesses dealing with global customers already know this. If your revenue crosses borders, the payment stack matters just as much as your banking setup, tax flow, and even your approach to secure and reliable international money transfers.
Stripe has a strong reputation for technical security, and that reputation is largely deserved. But the complete answer is more nuanced than “yes.” The practical view is that Stripe is safe in some ways that matter a lot, and risky in other ways that many glowing reviews barely mention.
Table of Contents
- The Billion-Dollar Question Every Merchant Asks
- What PCI DSS Level 1 actually means
- How encryption and tokenization reduce merchant exposure
The Billion-Dollar Question Every Merchant Asks
A founder usually asks “is stripe safe” at a very specific moment. Checkout is almost ready. Ads are queued. Customers are about to arrive. Then the uncomfortable thought shows up. What happens if fraud spikes, card data gets exposed, or payouts freeze right when payroll is due?
That concern is healthy. Payment systems deserve scrutiny because they sit between your customer’s trust and your company’s cash flow. If either side breaks, the damage is immediate.
Stripe is widely used because it makes card acceptance simple and because its security posture is taken seriously by larger businesses, not just startups. That matters. A processor handling sensitive payment data needs strong controls at the infrastructure level, not just a polished dashboard.
Safety for a merchant means two things at once. Customer payment data must stay protected, and the business must keep reliable access to revenue.
The mistake I see most often is judging safety only by breach risk. Merchants read about encryption, compliance badges, and fraud tools, then assume the whole problem is solved. It isn’t. Security for payment data and operational stability for payouts are related, but they’re not interchangeable.
For most standard online businesses, Stripe’s technical defenses are strong enough to pass a serious review. For higher-risk categories, cross-border models, or recurring businesses with uneven charge patterns, the practical risks widen. That’s where a simple yes or no answer stops being useful.
Stripe's Core Security Architecture Explained
Stripe’s technical security is strong where merchants need it to be strongest: card data collection, storage, transmission, and access control. If the question is whether Stripe has the baseline architecture expected from a major payment processor, the answer is yes. The more useful question is what that architecture protects well, and what it does not solve for a merchant.
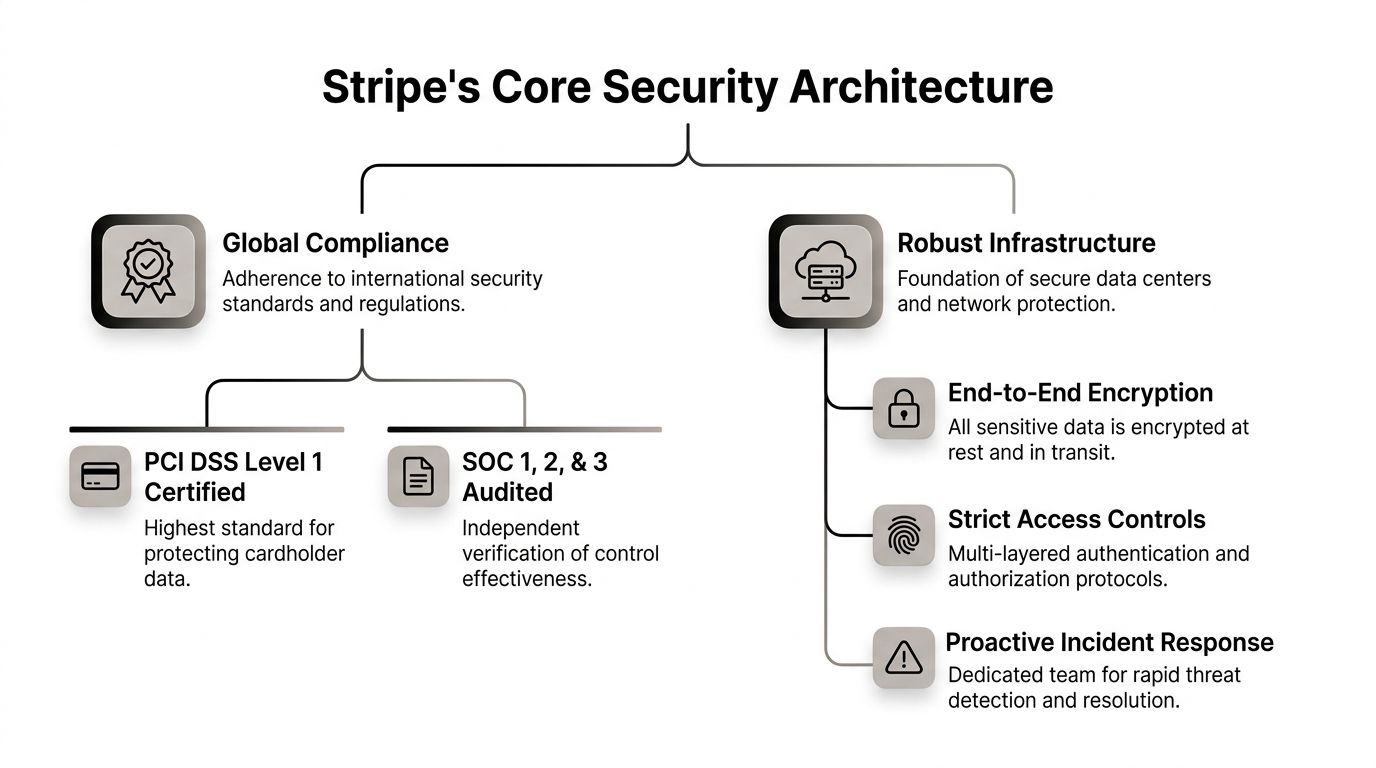
What PCI DSS Level 1 actually means
PCI DSS Level 1 is the highest compliance tier for handling cardholder data. For a business owner, that matters because it signals Stripe is operating under strict requirements for how payment data is protected, who can access it, how systems are tested, and how security controls are maintained over time.
Stripe maintains PCI DSS Level 1 certification. That does not mean a merchant is automatically compliant by signing up, but it does mean Stripe shoulders a large part of the card-data security burden if you use its hosted payment flows and tokenized setup correctly. A merchant-focused explanation of those responsibilities is in this overview of PCI DSS compliance for online payments.
In practice, PCI at this level usually means a few things merchants should care about:
- Controlled access to sensitive systems. Payment data should only be reachable by approved personnel and tightly scoped services.
- Ongoing testing and monitoring. Security controls need to be checked repeatedly, not installed once and forgotten.
- Documented procedures. Mature processors are expected to prove how they handle changes, incidents, and vulnerabilities.
That last point gets overlooked. Good payment security is operational discipline, not just encryption settings.
How encryption and tokenization reduce merchant exposure
Stripe also lowers risk by limiting how often your own systems need to touch raw card data. That matters because every extra server, plugin, admin panel, or employee workflow that handles card numbers expands your exposure.
Card data is protected in transit and at rest, and Stripe uses tokenization so merchants can process payments without storing full card details in their own environment. The practical benefit is simple. If your store runs on Stripe Checkout, Elements, or another well-implemented hosted collection method, your business handles less sensitive data directly.
Practical rule: The safest card data for your business is the data your systems never store.
That design choice is one reason developers and finance teams trust Stripe’s architecture. It reduces the attack surface on the merchant side. It also makes audits, incident response, and internal access control easier to manage.
If you want broader context on how processor controls fit into a wider security program, this comprehensive guide to fraud prevention and risk management is a useful companion read.
A simple way to view Stripe’s core security stack is below.
| Layer | What it does for the merchant |
|---|---|
| Compliance controls | Sets the baseline rules for handling cardholder data safely |
| Encryption | Protects sensitive data while stored and transmitted |
| Tokenization | Reduces the usefulness of intercepted payment data |
| Independent assessment | Confirms controls are reviewed and maintained over time |
For card-data security alone, Stripe clears the bar comfortably. Merchants still need to remember the bigger safety question. A secure processor can protect payment credentials and still create operational stress if risk controls later interrupt payouts or trigger account reviews.
Advanced Fraud Prevention and Authentication
Technical security protects stored data. Fraud prevention protects live transactions. That’s a different problem.
A secure processor can still leave merchants exposed if it doesn’t catch suspicious behavior before a bad payment turns into a refund, chargeback, or account review. Stripe addresses this with fraud tooling and authentication workflows that work during the transaction itself.

Fraud defense is an active system
The useful way to think about Stripe Radar is not as a checkbox feature, but as a screening layer. It evaluates signals around payment behavior and decides whether a transaction looks ordinary, suspicious, or worth additional scrutiny.
For a merchant, that matters because fraud rarely looks dramatic at first. It often starts as small transaction tests, mismatched billing patterns, repeated retries, unusual purchase velocity, or behavior that doesn’t fit your normal customer profile.
A broader comprehensive guide to fraud prevention and risk management is worth reading alongside processor-specific tools because fraud controls work best when payment filters, support policies, and internal review habits reinforce each other.
This is also why custom tuning matters. Generic settings can catch obvious abuse, but your fraud pattern may be specific to your product. A subscription business, digital goods store, agency retainer model, and community membership product don’t produce the same payment behavior. Merchants who want a practical overview of this kind of layered filtering can review payment fraud detection approaches for online businesses.
Where authentication matters most
Authentication adds another checkpoint. The best-known example is 3D Secure, often used to confirm that the person making the purchase is the legitimate cardholder. In European payment flows, Strong Customer Authentication also plays a major role, especially where regulation expects extra verification.
That extra friction can feel annoying in the moment. It can also save a merchant from a much bigger problem later.
Consider the trade-off:
- Less friction at checkout: Better for speed, worse when risky traffic rises.
- More authentication on selected payments: Slightly slower, but often safer for disputed or higher-risk transactions.
- Manual review for edge cases: Useful for unusual orders, but only if your team can respond quickly.
If your business attracts international traffic, don’t judge checkout quality only by how fast the payment form appears. Judge it by how well the system filters bad payments without blocking too many real buyers.
The strongest merchants don’t rely on fraud tools alone. They pair processor rules with clear product descriptions, visible refund terms, and support replies that arrive before a cardholder gives up and files a dispute.
The Other Side of Safety Account Holds and Payout Risks
This is the part many reviews skip. A processor can be secure and still feel unsafe to a merchant if revenue gets trapped in review.
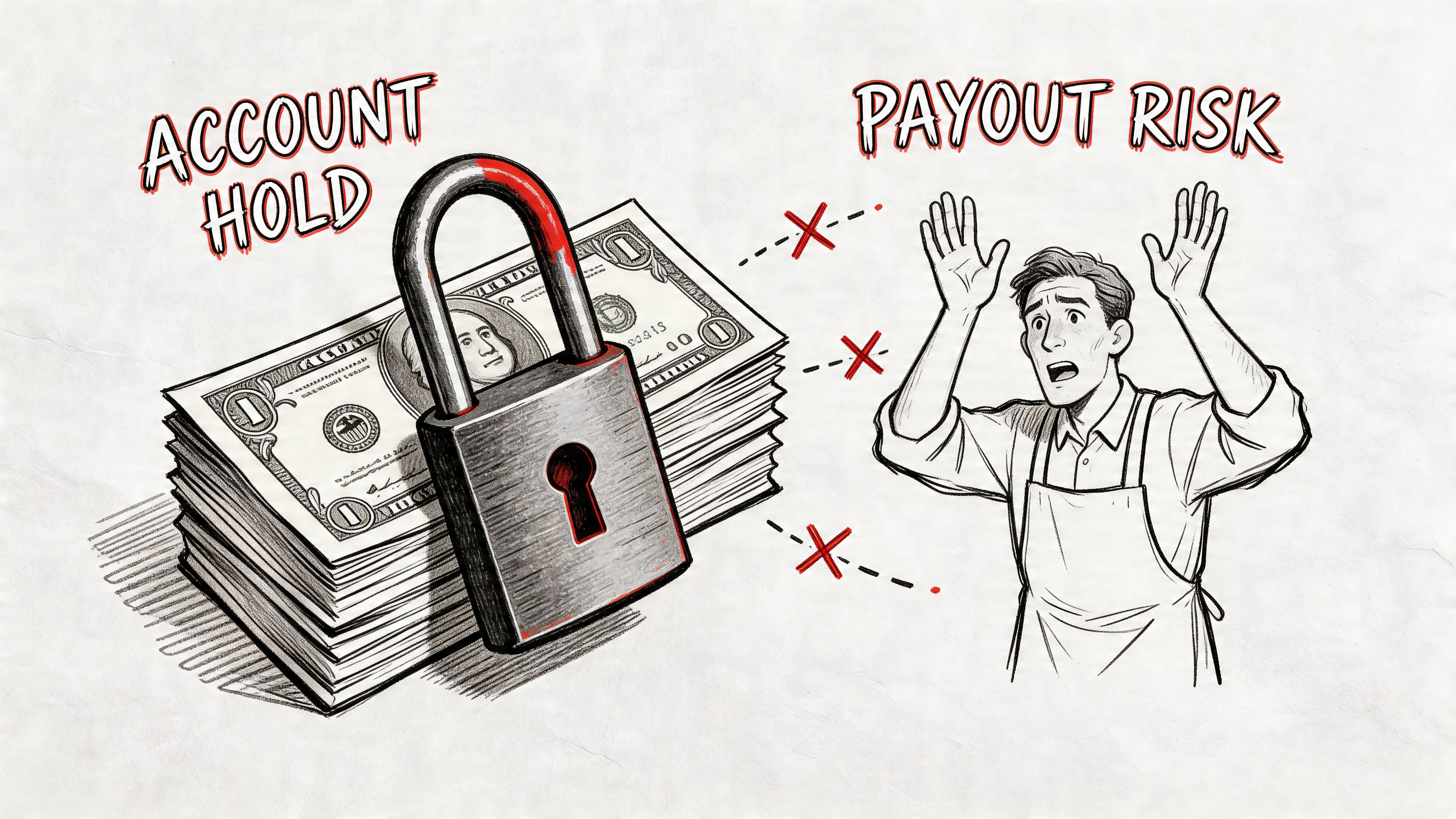
The practical version of “is stripe safe” isn’t only about card theft or database breaches. It’s also about whether your business can count on predictable access to funds. For many merchants, especially those selling internationally or through subscriptions, safety translates into a cash flow question.
Why holds happen even when nothing was hacked
Stripe, like other processors, runs risk reviews. Those reviews aren’t necessarily signs of fraud or a compromised account. Often they’re triggered by patterns the system interprets as increased risk. A spike in volume, unusual refund behavior, cross-border sales, subscription churn, or a mismatch between business profile and transaction activity can all make a processor cautious.
Merchant complaints on Reddit and Trustpilot frequently describe frozen funds tied to opaque risk reviews rather than security breaches, with some merchants reporting waits of over 6 months, and a source discussing this issue notes that projected post-2025 PSD3 changes could increase holds by 15% for certain business types in this analysis of Stripe hold risks.
That doesn’t prove every complaint is fair. Some merchants understate their risk profile. Some accounts are flagged for valid reasons. But the pattern matters because it highlights a blind spot in most “Stripe is safe” articles. They discuss encrypted card data and skip the operational fact that processors also protect themselves.
Here’s the merchant-facing reality:
- High-risk interpretation can widen quickly: A normal launch spike may not look normal to a risk engine.
- Subscription models face extra scrutiny: Recurring billing creates downstream exposure if refunds and disputes rise later.
- Cross-border flows are harder to explain: Multiple jurisdictions, customer locations, and card issuers create more review points.
Cash flow safety matters too
The video below covers the issue from the merchant’s perspective.
When a business owner says a payment setup feels unsafe, they often mean they can’t tolerate payout uncertainty. Payroll, ad spend, supplier invoices, and contractor payments don’t pause because a processor opened a review.
That’s why I treat technical security and settlement reliability as separate criteria. Stripe scores well on the first. Depending on your model, the second may need more caution.
If account stability is a major concern, it helps to study the common patterns behind a Stripe frozen account and payout review before volume scales. It’s easier to reduce triggers early than to argue after a hold is in place.
For businesses that want a different payout structure, Suby is one option to evaluate. Suby provides an API that lets businesses accept payments by card or crypto, while merchants receive USDC. It also offers native Discord and Telegram integrations for subscriptions, paid access, and online communities. The core model is simple. Users pay with cards, businesses receive USDC. That changes the settlement side of the equation because the payout flow doesn’t depend on the same bank-based timing and hold patterns merchants often worry about.
Data security protects the transaction. Payout design protects the business model.
Navigating Disputes and Chargebacks
Chargebacks are different from account holds. A hold affects your account access. A chargeback affects a specific transaction after the customer’s bank gets involved.
Many merchants assume Stripe decides the outcome. It doesn’t. Stripe facilitates the process, collects your evidence, and passes it through the card network and issuing bank workflow. The final decision usually sits outside the processor.
What Stripe does and what it doesn’t do
Stripe can notify you about disputes, give you a deadline, and provide an interface for submitting evidence. That’s helpful. But it doesn’t turn a weak case into a strong one.
The merchant usually loses when the original transaction was poorly documented or the customer experience was sloppy. Common examples include unclear billing descriptors, vague refund terms, a trial that rolled into a paid plan without enough notice, or digital delivery that can’t be proven.
A simple distinction helps:
| Situation | What matters most |
|---|---|
| Fraud claim | Proof the legitimate cardholder authorized the transaction |
| Product not received | Delivery evidence and fulfillment records |
| Service dissatisfaction | Contract terms, usage records, and prior communication |
| Recurring billing complaint | Clear consent, renewal notice, and cancellation path |
What improves your odds in a dispute
You can’t eliminate disputes, but you can reduce preventable ones and respond better when they happen.
- Use recognizable billing descriptors: If customers don’t recognize the charge, they often call their bank before they contact you.
- Show policies before payment: Refund and cancellation terms should appear before the customer pays, not only in a footer.
- Keep delivery evidence organized: For digital products, that can include login records, download events, or account access history.
- Answer support tickets quickly: A frustrated customer often escalates because nobody replied in time.
- Tailor evidence to the claim: Don’t upload a pile of screenshots. Submit material that directly addresses the dispute reason.
A chargeback response works best when it reads like a clean timeline, not a desperate argument.
One more point matters. Some disputes are worth fighting, others aren’t. If the evidence is thin, forcing every case into representment can waste time and increase stress for no real return. Good operators know when to contest and when to tighten the process instead.
How Merchants Can Actively Enhance Their Security
Processors handle a lot, but merchants still create many of their own risks. Weak account controls, confusing checkout language, and poor support habits can undo the benefits of a secure platform.

Account hygiene comes first
Start with the boring controls. They prevent a surprising number of avoidable problems.
- Enable two-factor authentication: Anyone with payout or admin access should use it.
- Use unique credentials: Shared logins create accountability gaps and make investigations messy.
- Limit permissions by role: Finance, support, and developers shouldn’t all have the same account powers.
If your team handles customer questions around billing, support workflow matters too. A review of Stripe support integration tools for operations teams is useful because a lot of payment risk begins as unresolved support friction, not pure fraud.
Operational habits reduce avoidable risk
The second layer is how you run the business day to day. Security isn’t only technical. It’s procedural.
A practical merchant checklist looks like this:
- Review your checkout copy so buyers know exactly what they’re purchasing.
- Make cancellation and refund paths obvious for subscriptions and services.
- Watch for unusual transaction patterns and tighten fraud rules when something changes.
- Document fulfillment events so dispute evidence exists before you need it.
- Keep compliance information current if your business model, location, or ownership changes.
The merchants who handle payment risk best aren’t always the most technical. They’re usually the clearest communicators.
If you sell globally, this becomes even more important. Cross-border customers are less forgiving when charge descriptions are unclear, support is slow, or payment confirmations feel inconsistent.
A Balanced Verdict and Future-Proofing Your Payments
So, is Stripe safe?
On technical security, yes. Stripe’s controls, compliance posture, encryption practices, and transaction defenses make it a credible and broadly trusted processor for online businesses. If your concern is whether card data is being handled with serious security discipline, Stripe clears that bar.
The more honest answer is that safety has two layers. Stripe looks strong on protecting payment data. It can be less predictable when the issue shifts from data security to account reviews, payout timing, or fund access for certain business types.
That doesn’t make Stripe uniquely bad. It makes it a real payment processor with real risk policies.
For merchants with conventional risk profiles, Stripe is often a reasonable choice. For international SaaS companies, online communities, subscription businesses, and operators who highly value predictable settlement, future-proofing payments may mean looking beyond the traditional card-processor-plus-bank model.
That’s where a different structure can make sense. Some businesses now want customers to pay with cards while the business receives USDC directly, with fewer payout delays and less banking friction. That model is especially relevant for internet-native products, global subscriptions, and creator businesses running paid access in Discord or Telegram.
If you want to explore that payout model, Suby provides an API that lets any business accept payments by card or crypto, while receiving revenue in USDC. It also offers native integrations for Discord and Telegram, which makes it practical for subscriptions, paid access, and online communities. The core flow is simple. Users pay with cards, businesses receive USDC.